Troubleshooting the Atmos Agent
This article describes how to troubleshoot specific Atmos Agent issues.
To learn how to troubleshooting basic Atmos Cloud issues, click here.
Unable to Install the Atmos Agent
On Mac and Windows OS platforms, users need to be an administrators to install the Atmos Agent or when the Atmos Agent is deployed using the Electronic Software Distribution (ESD) tools.
If the correct permissions are not given to the agent on Mac, in the Axis Debug UI Log the error "[APP] [Error] Failed forward message: config.Get to connector. error: dial tcp 127.0.0.1:7777: connect: connection refused" may be reported along with a series of similar errors.
Recommended Action: If you do not have administration rights to install the Atmos Agent, contact your IT organization for assistance.
Atmos Agent Installed but Security Permissions Require Approval (macOS)
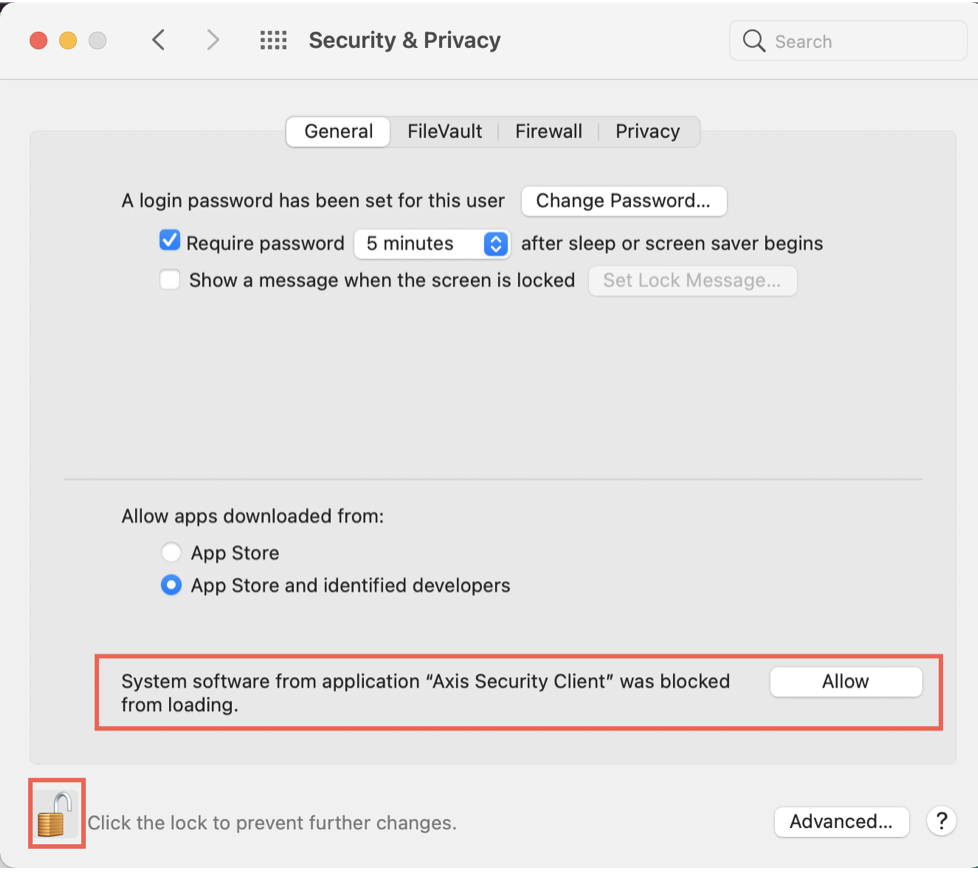
On macOS platforms, some users might have administrative privileges to successfully install the Client but still need to set their security permissions to Allow the Atmos Agent.
NoteIf this setting is not allowed, the Atmos Agent will run but will not be able to create the network interface.
To allow the Atmos Agent in your security permissions in macOS:
- Go to System Preferences > Security & Privacy > General.
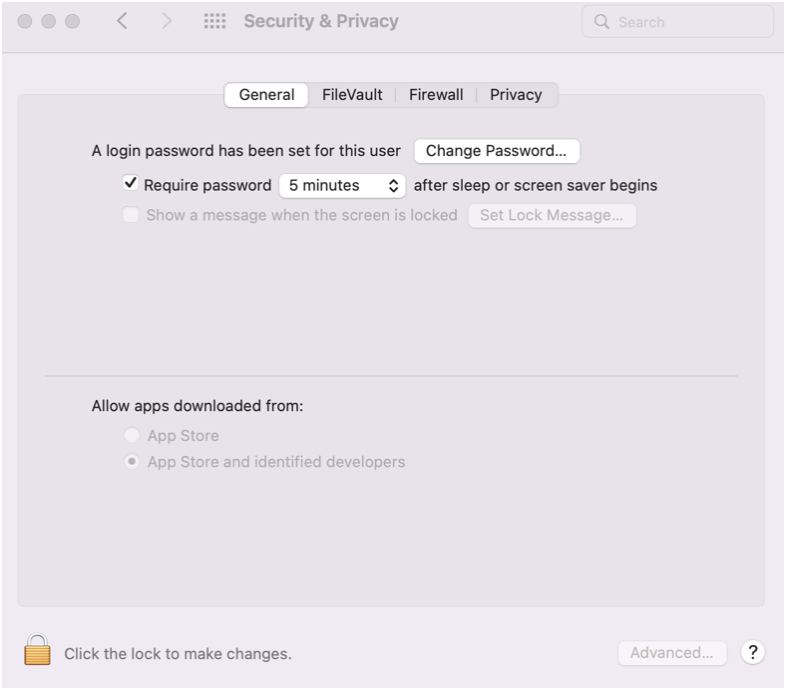
- In the lower left of the window, click on the lock icon to unlock this window and make changes to allow the Axis Client.
ImportantBefore you click on this lock consider the following:
This window only stays open for short periods of time and then closes. If you don’t click on it in time, you might need to reinstall the client.
Atmos Agent Opens but User Login Screen is Empty or Doesn’t Display
Once a user has the Atmos Agent application running properly on a system, typically the next set of issues are all network-based. There could be a security tool installed on the user’s device that is a host-based firewall or proxy, or maybe the user is on an enterprise network that has these service tools (firewalls, proxies) to get to the Internet.
If any of these applications or network services block some or all of the communication required between the Atmos Agent and Axis Cloud, Axis communication will not work.
The Atmos Agent displays a built-in “web browser” for the Identity Provider that your administrator has configured in their Axis tenant (such as Axis IdP, Okta, and AzureAD).
In this scenario, the user opens the Atmos Agent, types in their workspace (tenant) name, but then nothing happens or a popup Windows is displayed where the authentication should redirect you to your IdP but instead this a window is empty.
To troubleshoot Atmos Agent portal issues:
- Determine if it is a host or network-based issue.
-
Ask the user to try using the Atmos Agent from another network, their home network instead of the corporate office.
-
If this issue persists then something installed on the device is blocking Axis network connectivity. For example, if you have trouble on your corporate network and switched to your home network, you have device issues. If this is the case, contact your IT Administrator to see if there is any host-based security software; for example, firewall or antivirus, that is running on your system that needs to be addressed.
-
If this issue goes away, then most likely the problem is the network in the office that has a firewall or proxy blocking Axis connectivity.
- Work with your IT organization or security administrator to review the logs of either your host or network-based firewalls and proxies the device would go through to see if it is blocking the Atmos communication. To learn more about Firewall rules that are required, click here.
Atmos Agent Enrolled Successfully but Users Can’t Access Applications
If the Atmos Agent enrolls successfully but some applications do not work and connectivity is working as expected, a common cause is either a misconfigured policy rule or an application server issue.
See also:
- Best Practices for Configuring a Policy
- Naming Applications, Policies, Connector Zones, & Application
Common Policy Rule and Application Misconfigurations Checklist
Use the following table as a guide to to troubleshoot policy rule (conditions) misconfigurations.
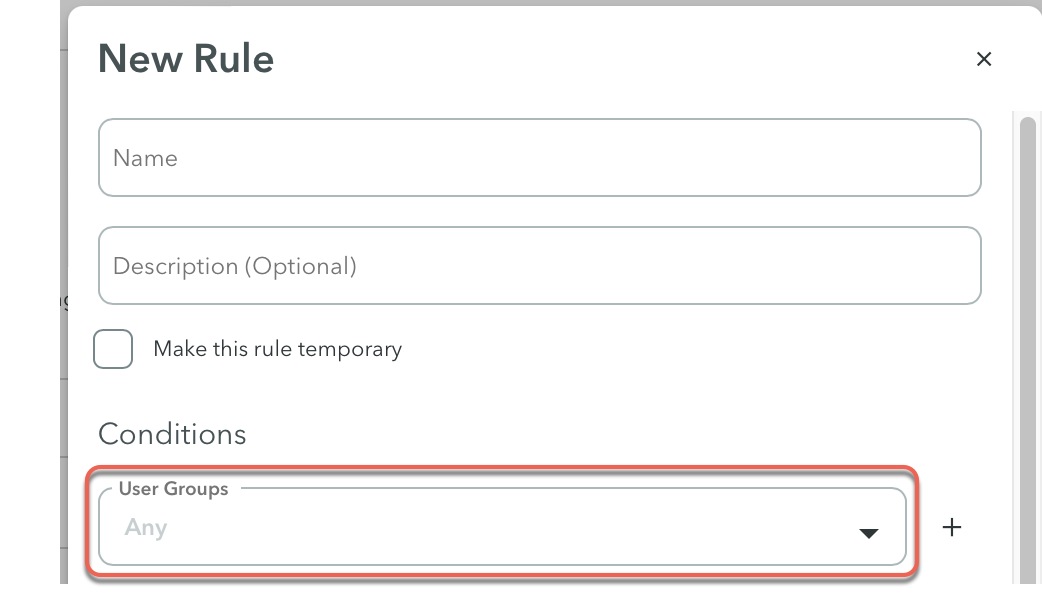
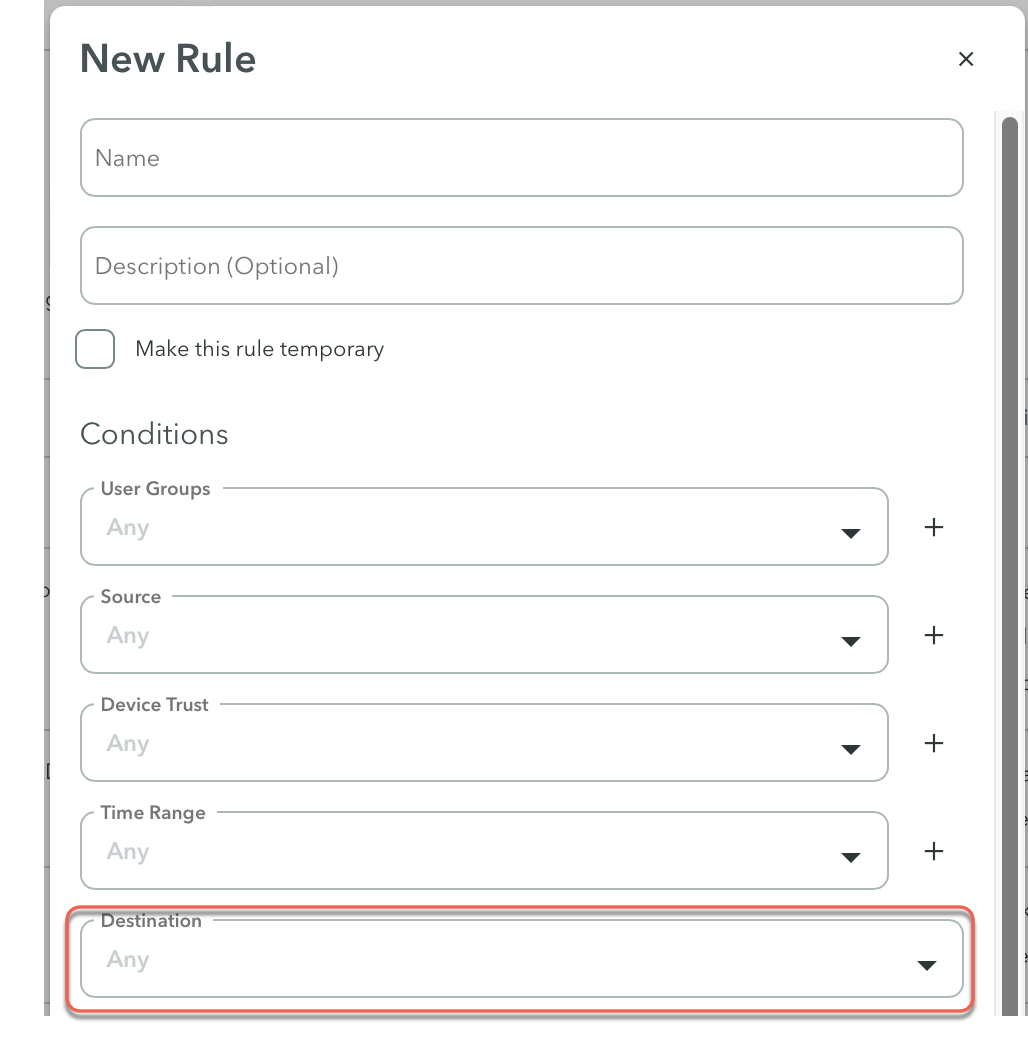
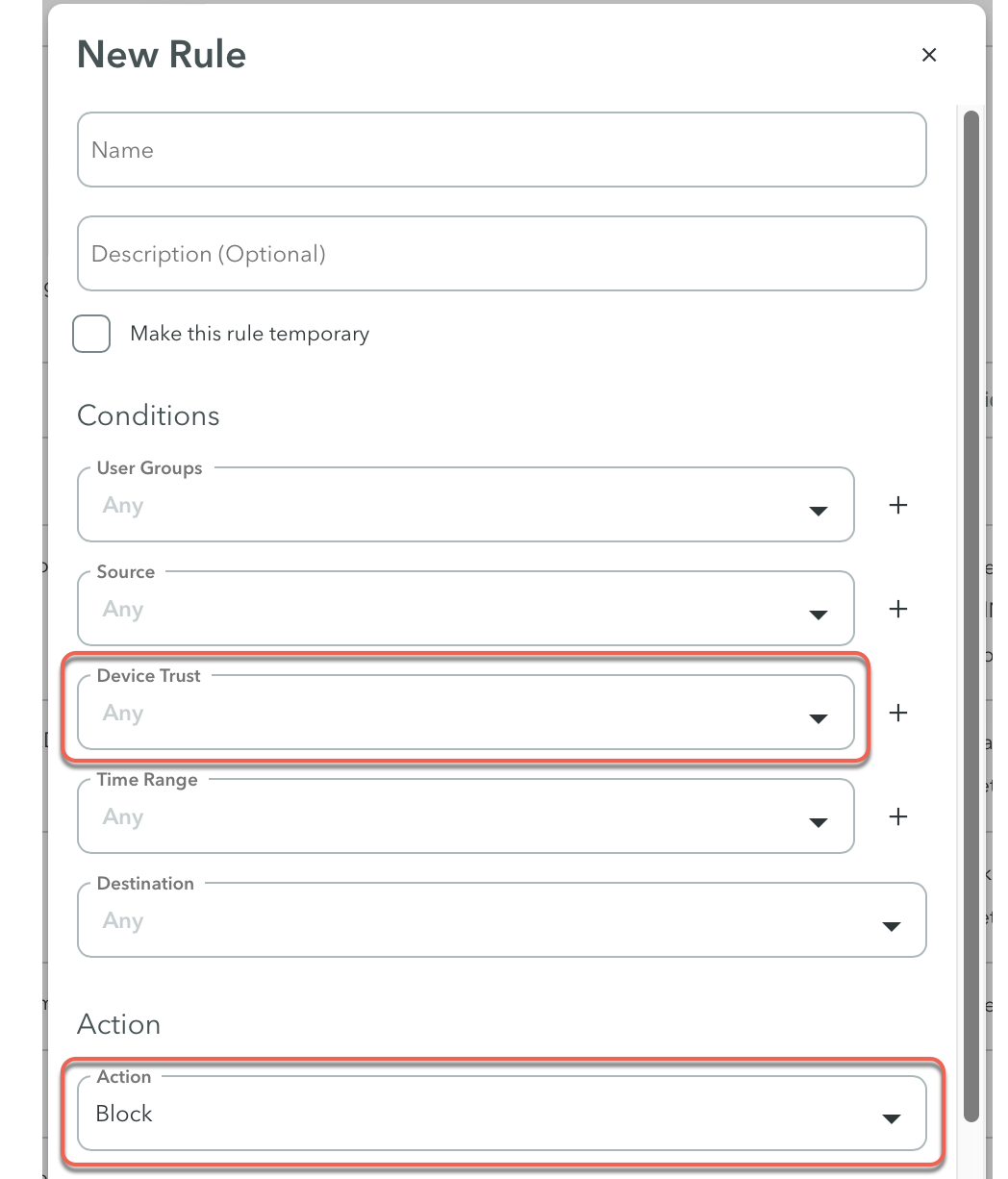
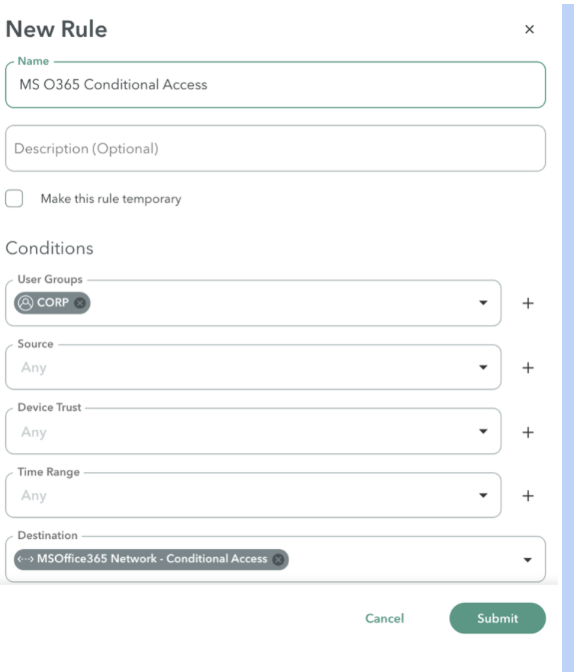
Here is a policy rule screenshot for reference.
| Task | Checked? | |
|---|---|---|
| 1 | Verify that the user’s identity is mapped to application with a rule at the Policy > Rules. In the Conditions, check the User Groups. Are my users connected to an application through a rule?
| |
| 2 | In the Destination, verify that the application mapped to the destination.
| |
| 3 | In the Source condition, verify that the user is coming from an approved source specified in the Source rule. | |
| 4 | If the Device Trust is configured (Optional setting), verify that the user’s device is compliant with the configured device trust profile.
To learn more, see Device Trust. | |
| 5 | In the Action, is this rule set to Block instead of Allow. | |
| 6 |
| |
| 7 | After checking steps 1-7, if you are unable to resolve this issue, contact Customer Support. |
Updated 3 months ago