About Network Range
Network Range enables access to multiple applications in an IP range or under a DNS wildcard, without publishing a unique application for every server in the range. It also allows admins to grant access to applications or protocols that are unavailable for clientless access.
A network range includes IP addresses, IP ranges, FQDN/URLs, or DNS wildcards. The Axis Client downloads the addresses from every network range to which it has access and updates the OS routing table.
NoteThe users will not communicate with the original server's IP address but with the "fake IP" generated by the Axis Client.
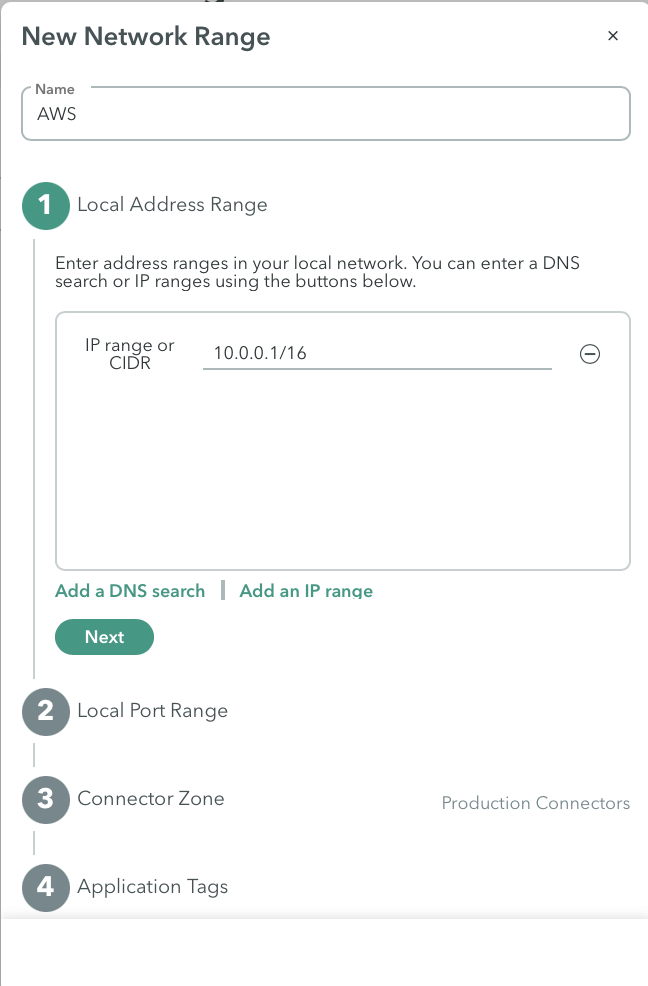
If end-users need to access the original IPs in the private network, the admin should replace the DNS wildcard with the servers' IP range.
Example: Network Ranges Use Case
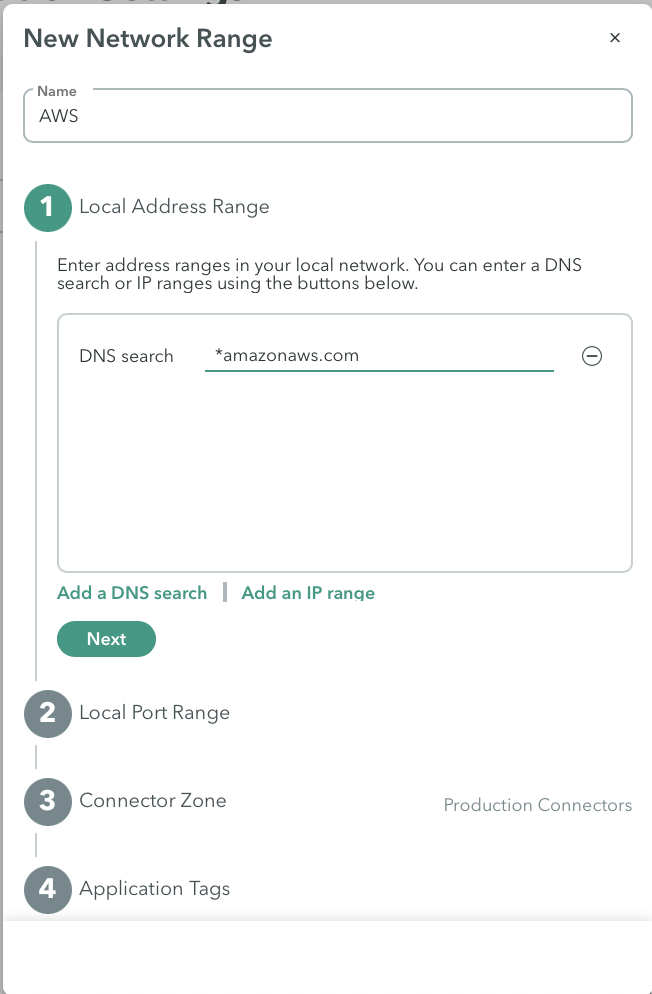
The IT admins want to grant their department access to all AWS servers in their private network. Knowing the servers' addresses are in the format "XXX.amazonaws.com", they create a network range with the DNS wildcard "*.compute.amazonaws.com". After creating a policy rule granting the "IT department" group access to the new network range, every member can access the AWS servers using their URL address.
ICMP Requirements
For information on the requirements needed to enable ICMP, click here.
Which ICMP Commands are Supported?
For information on which ICMP commands are supported, click here.
Network Range Visibility
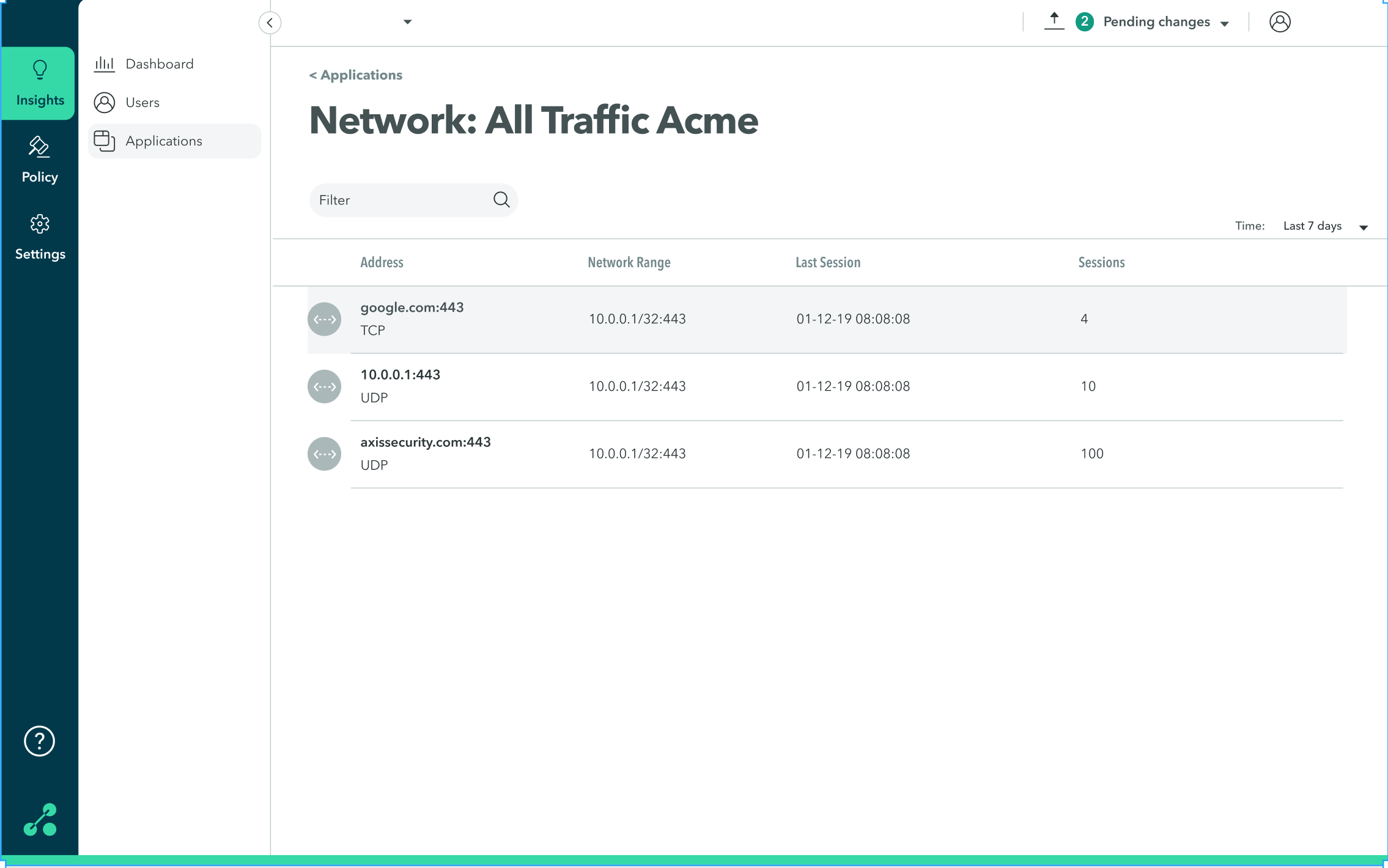
Administrators can see when a user connects and disconnects in destinations within the Network Range at the Insights > Applications screen. This is useful for learning which destinations were visited and creating specific applications for these destinations thus controlling user activity and increasing security.
The Insights > Applications screen displays the destinations accessed within the Network Range:
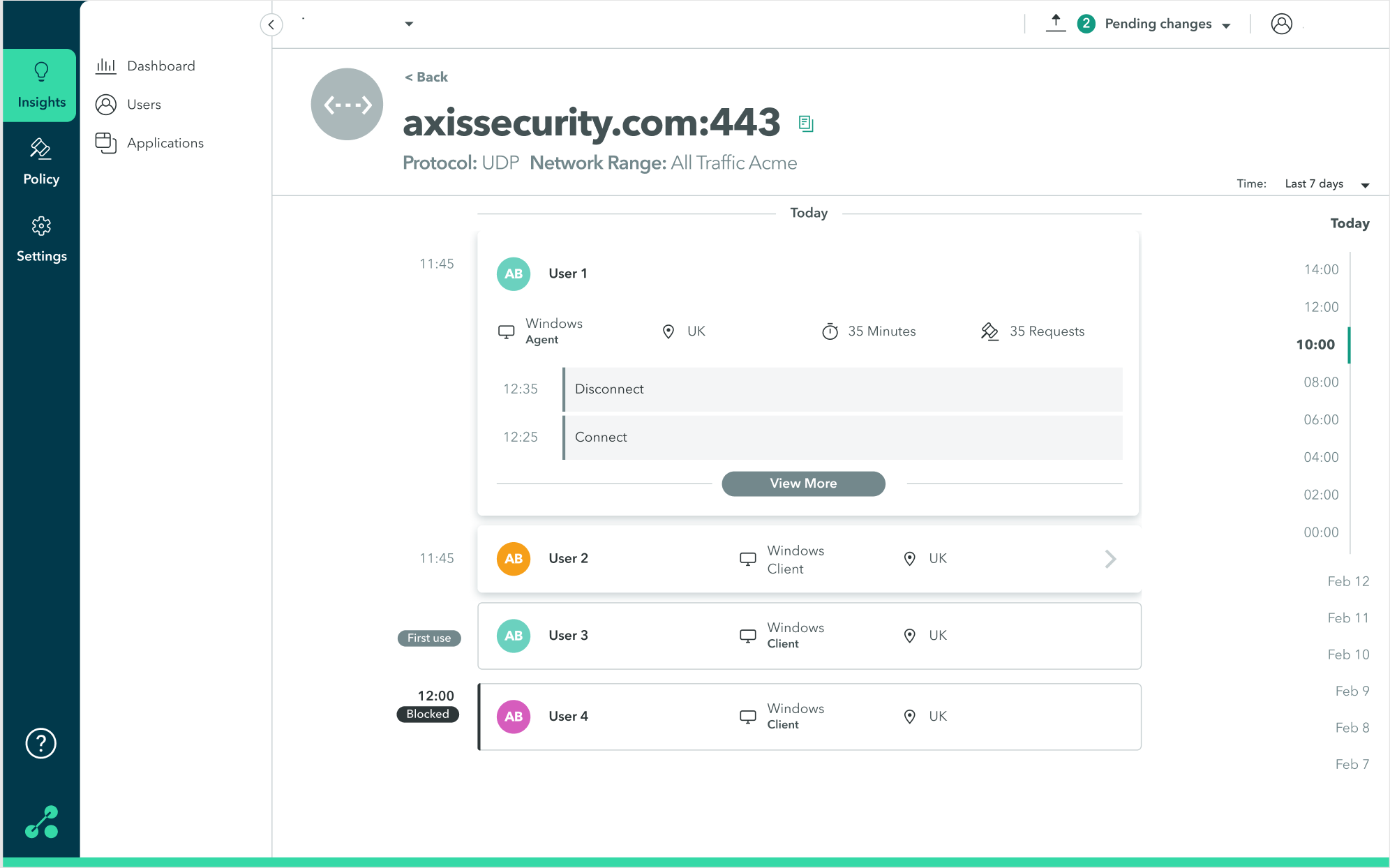
For each destination, the Insights Dashboard displays information about users' activity:
Updated 3 months ago
