About Policies
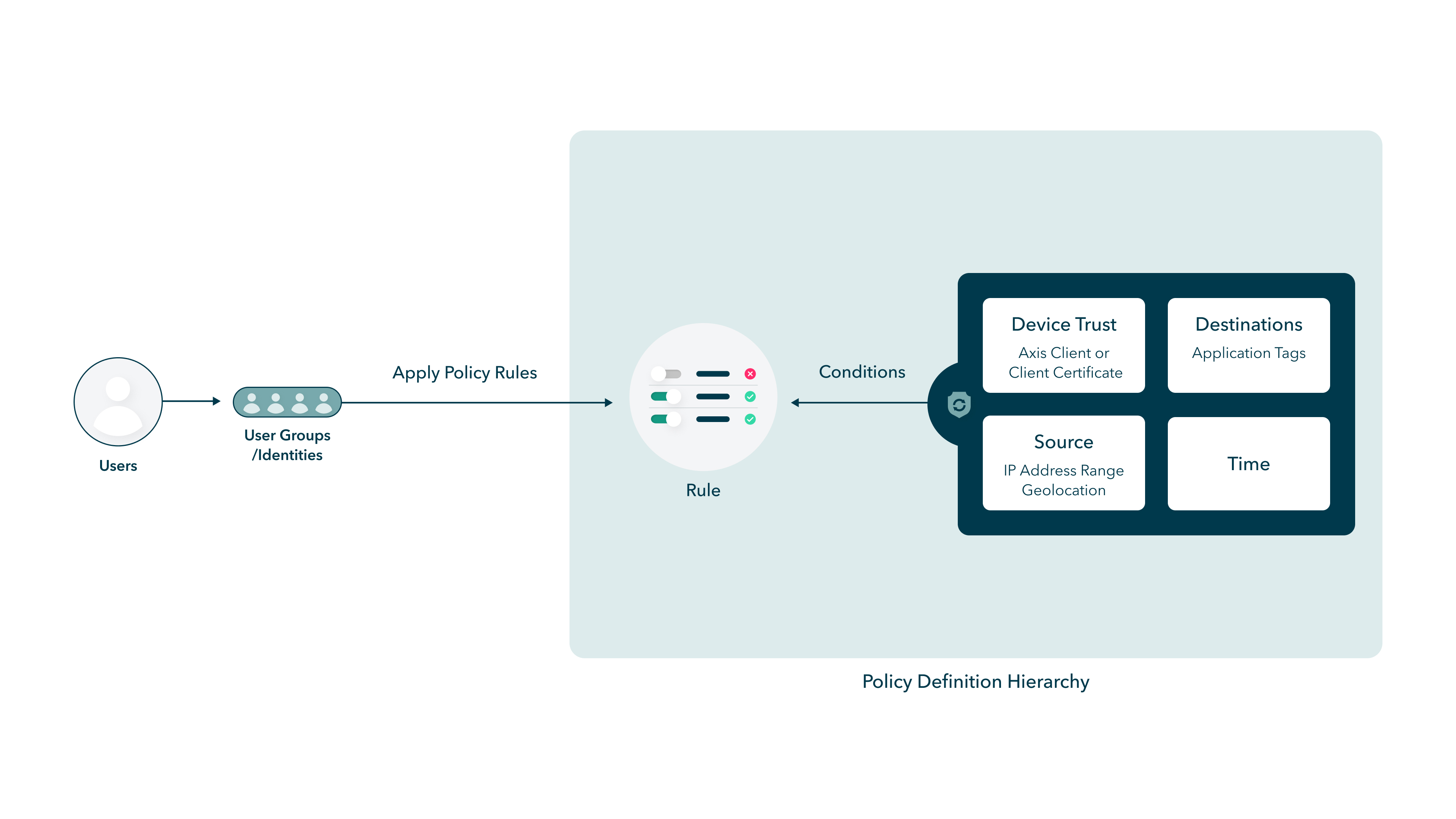
A Policy is a collection of rules which provide granular access to your apps depending on a range of parameters. For example, access can be defined based on the destination application groups of the requester.
Atmos enforces policies continuously; when a user's session no longer adheres to a policy rule, it is terminated immediately. Click here to learn more about continuous policy enforcement.
Policies define the following:
- Who can access a application
- Which applications users can access
- When users can access a application
- From where users can access an application, geo location; IP address range
- If users are allowed to access an application, based on the device posture, i.e. it is patched, or does it have a firewall enabled.
- The level of access that a user can have during the connection, i.e. are they allowed to perform certain actions and how often they have to re-authenticate.
- Whether users are explicitly blocked from accessing one or more applications.
- How users can access an application (Axis Agent, Agentless)
A rule consists of a set of modular policy objects called Conditions. Admins can either create Conditions in advance, for later use, or in the course of defining Policy Rules. Admins can also create a Security profile to restrict user activity by protocol. For example, a Rule may block a file transfer during an RDP connection based on a more restrictive Profile.
Conditions include:
- Locations. For more information, see Configuring Locations.
- Source IPs. For more information, see Adding Source IPs.
- Time Ranges. For more information, see Adding a Time Range.
- Device Postures. For more information, see Device Trust and Configuring the Atmos Agent Device Posture.
Security Profiles are part of a policy and include:
Architecture
The following diagram describes the policy definition hierarchy architecture for creating a policy.
The Policy Table
The Policy table presents information about the different rules in the tenant at-a-glance:
NoteYou can filter rules by hovering over a field and clicking the filter icon.
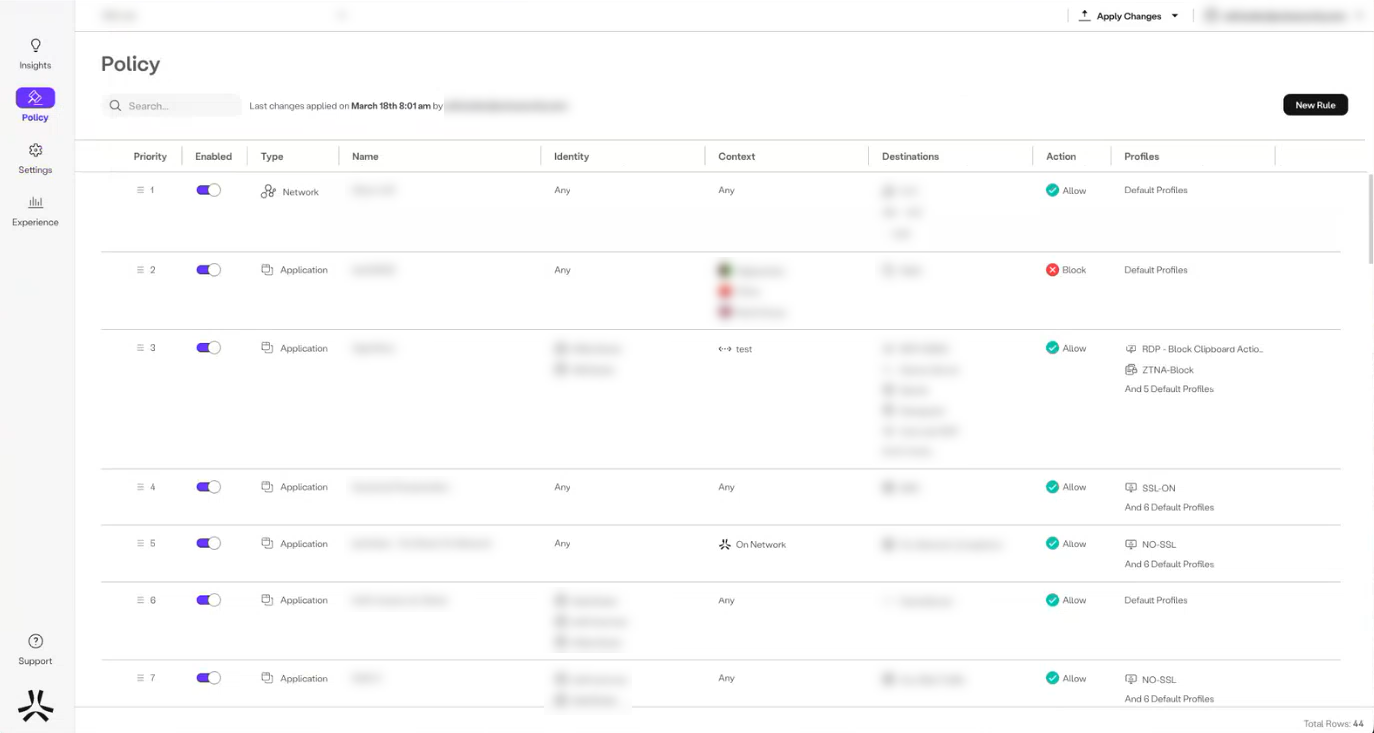
- The Prioritycolumn allows you to change priorities by clicking the corresponding icon and moving the rule to another location in the list.
- The Enabled column allows you to enable or disable a rule using the toggle.
- The Type column provides information on the type of rule. For example, Network (firewall rule), or Application.
- The Name column displays the name of the rule.
- The Identity column displays the users to whom the rule is applicable.
- The Context column provides information about device trust (device posture and agent certificates), Source IPs, geolocation, and time ranges.
- The Destinations column provides information about the applications or application tags associated with the rule. If the rule is network-based, the Destinations columns also displays information about the ports and protocol.
- The Action column displays whether the rule is allowed or blocked.
- The Profiles column provides information about the security profiles associated with the rule.
Note:To edit or delete a policy, hover over the rule and select the edit or delete icon on the right.
Updated about 1 month ago
